A small & mighty digital agency™ that helps
courageous
brands.
What is courage?
Risk. Boldness. Confidence. Resolution.
We believe in the brilliant undiscovered. Those who take a chance despite fear. Those who do something in the face of challenges. Those who own who they are and leverage it. Those who have the willingness to apply strategy and sacrifice to accomplish their goals.


Your fan club.
Marketing, traveling, branding, writing, photography, research, coding and cooking. Our team is diverse in our abilities and interests. This blend of talents and experience makes us come at things from all angles, which is good, because no two challenges are the same.
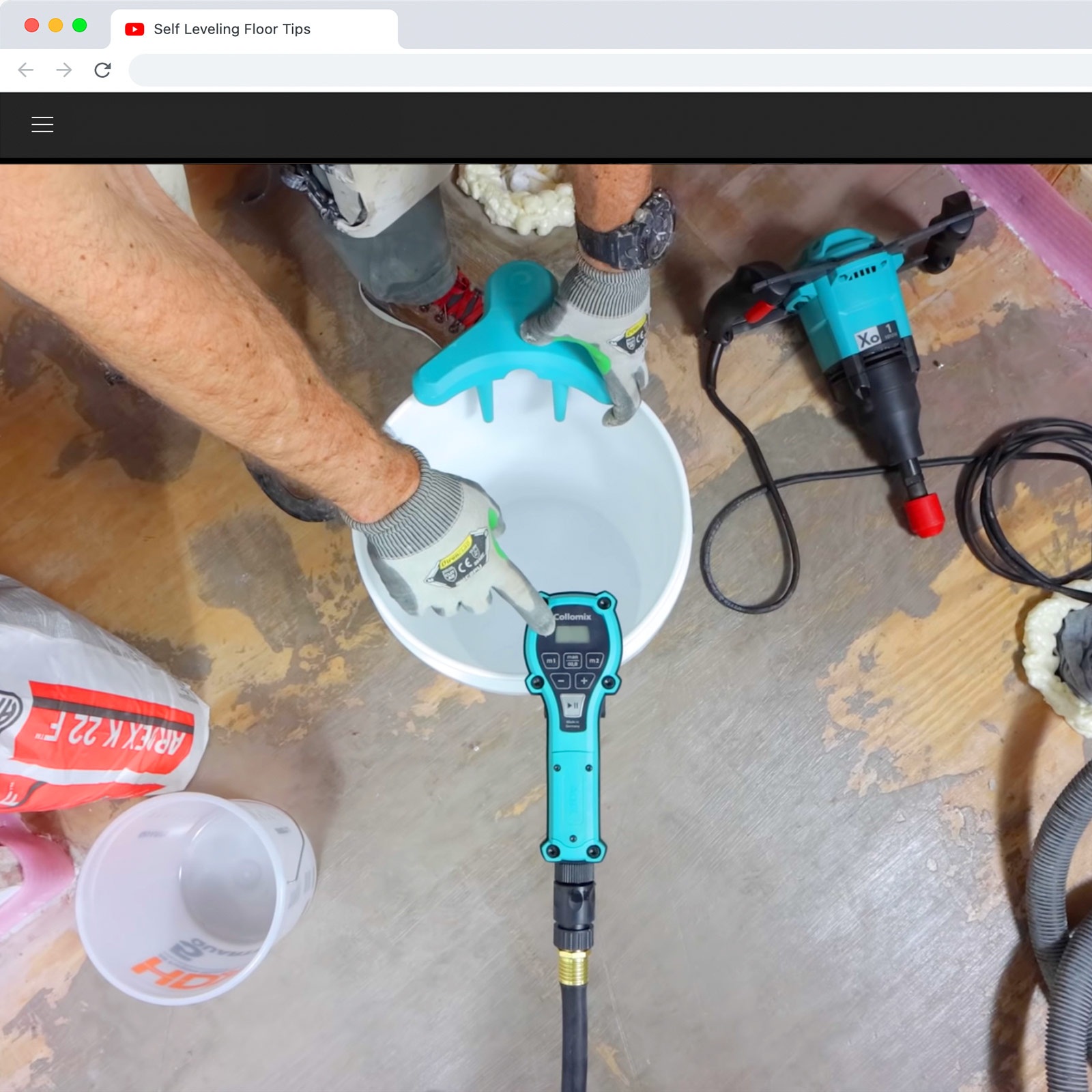
Hi! This is us. Whether launching a brand for a startup, designing an online game with real-world activations, filming from a zipline, or taking exploratory trips overseas, we are willing to do anything to help you be courageous. With over 20 years of experience, we are mighty but remain small so that you get personal attention and always know who you’re talking to.
Building together.
It’s about you. Defining you, building you up and helping you succeed. Everything we do...we do it for you (long live Bryan Adams).
We are thinkers, designers, engineers, wordsmiths… and your friends. Everything we do is about telling your story honestly and effectively. Using research and strategy, we create and build you into a brand that gets your message to the right audience loud and clear.

Are we the agency for you?
We have a lot to offer, but we know you have a lot to lose.
Before you swipe right, you want to make sure this is gonna work out. We get it! Compatibility is key. So, we’ve created a little quiz to help you decide if we are a good fit. Like a dating app for digital agencies. Swipe right?
Meet the courageous.
Here are some of the mighty brands we’ve worked with.